Tunnel all Microsoft 365 traffic with VMware Tunnel
This blog post detail how to tunnel all traffic for Microsoft 365 applications on iOS and Android, it explains what the necessary steps are to be able to do so.
I assume that VMware Unified Access Gateway is deployed with Tunnel services activated and proven to be functional.
Technical detail
Microsoft 365 applications can all be tunnelled entirely, however the support for authentication requires to have a specific deployment. Microsoft 365 applications always use Authenticator code even if Authenticator is not installed by doing so the application name is changed to Authenticator this enforce the need to add Authenticator to the Device Traffic Rules, also each application may behave differently if Authenticator is not installed. As a result, it’s highly recommended to deploy Authenticator, it will also be used as anchor point for authentication across all Microsoft 365 applications.
Flows
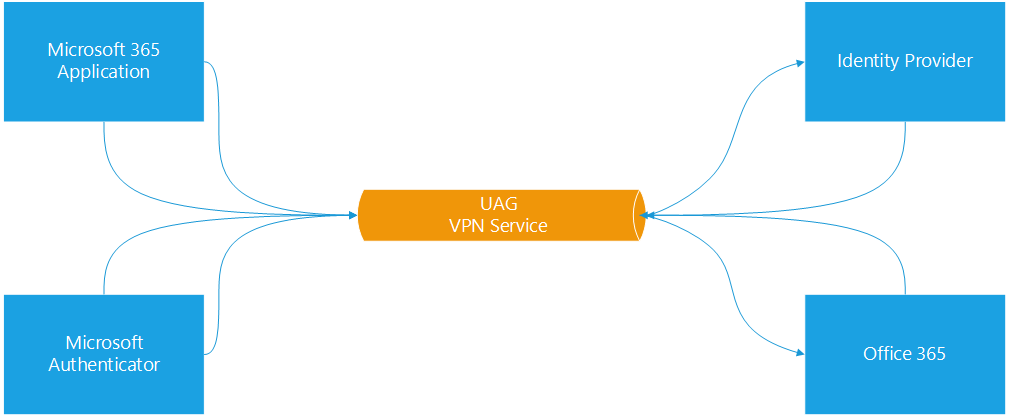
Network flow
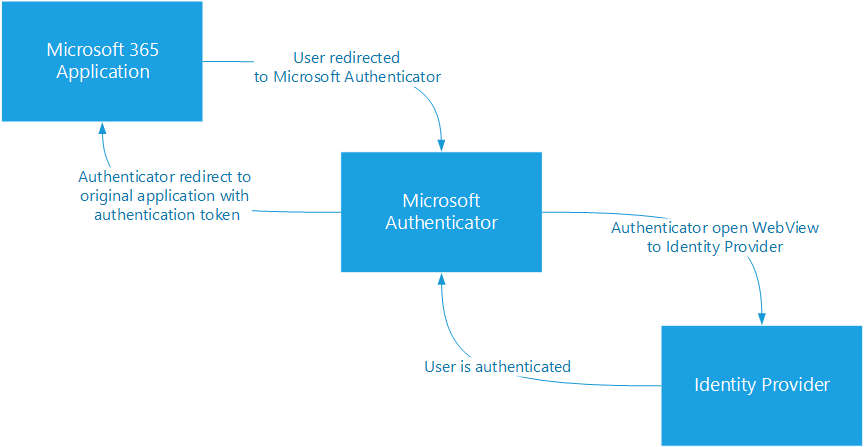
Authentication Flow
Pre-requisite
- Workspace ONE UEM any supported version
- Unified Access Gateway (UAG) any supported version
- VMware Tunnel
Applications Deployment
The only requirement is to have Microsoft Authenticator and any other Microsoft application deployed automatically via MDM as the VPN profile need to be applied to the application before adding the application to the device traffic rules.
If applications can be installed by the user directly make sure the “Make App MDM Managed if User Installed” is enabled, so management is taken upon enrolment.
Device Traffic Rules
There are 2 options to configure the Device Traffic Rules:
- Have a dedicated rule to tunnel all traffic Microsoft 365 applications and Microsoft Authenticator
- Use the default rule to tunnel all traffic
If Android Mobile SSO is used, keep Mobile SSO traffic rule take priority over any other rule.
Dedicated Rule
Add a rule with all Microsoft applications with TUNNEL as the action and * (wildcard) for destination.
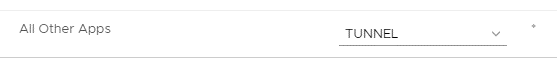
Default rule
On the default traffic rule change the default action to TUNNEL instead of BYPASS
vExpert, blogger and VMware champion. Worked as a Microsoft consultant for a partner before joining VMware via Airwatch in 2015.


Mirco Reimer
Thanks for the article – are all the custom settings for tunnel somewhere documented in a condensed way instead of finding them here or there in blogs or the documentations?
Camille Debay
Not that I know of most of those settings should come up at some point in the profile UI, however it would indeed be useful to have a centralised page, I will discuss it with the doc team.
You can also share your feedback directly in the documentation.